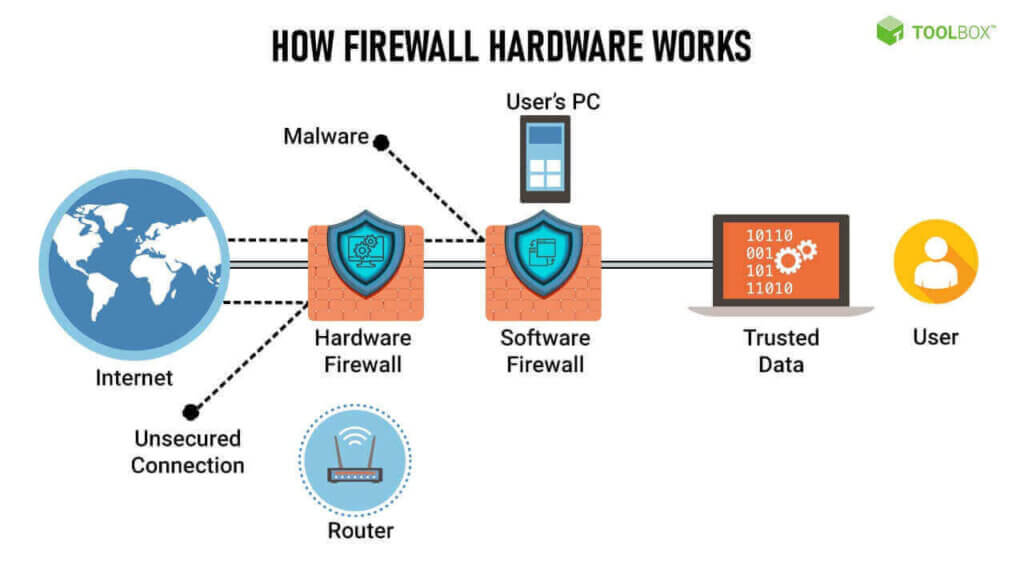
AA firewall is your network’s first line of defense. The basic purpose of a firewall is to prevent uninvited guests from browsing your network. A firewall can be a hardware device or software application that is usually located at the perimeter of a network to act as a gatekeeper to all incoming and outgoing communications.
Firewalls allow you to establish specific rules to identify the traffic that should be allowed to enter or leave the private network. Depending on the type of firewall implemented, you can restrict access to only certain IP addresses and domain names, or you can block certain types of communication by blocking the TCP/IP ports it uses. is a network security system that monitors and controls incoming and outgoing network traffic based on Firewalls allow you to establish specific rules to identify the traffic that should be allowed to enter or leave the private network. Depending on the type of firewall implemented, you can restrict access to only certain IP addresses and domain names, or you can block certain types of communication by blocking the TCP/IP ports it uses.
How its work?
Firewalls carefully analyze incoming traffic based on pre-established rules and filter traffic coming from unsecured or suspicious sources to prevent attacks. Firewalls guard traffic at a computer’s entry point, called ports, which is where information is exchanged with external devices. For example, “Source address 115.168.3.x is allowed to reach destination 115.168.2.x over port 22.”
Think of IP addresses as houses, and port numbers as rooms within the house. Only trusted people (source addresses) are allowed to enter the house (destination address) at all—then it’s further filtered so that people within the house are only allowed to access certain rooms (destination ports), depending on if they’re the owner, a child, or a guest. The owner is allowed to any room (any port), while children and guests are allowed into a certain set of rooms (specific ports).
Types of firewall
Firewalls can either be software or hardware, though it’s best to have both. A software firewall is a program installed on each computer and regulates traffic through port numbers and applications, while a physical firewall is a piece of equipment installed between your network and gateway such as Fortinet FortiGate Firewall, Sophos, SonicWall etc .
Packet-filtering firewalls, the most common type of firewall, examine packets and prohibit them from passing through if they don’t match an established security rule set. This type of firewall checks the packet’s source and destination IP addresses. If packets match those of an “allowed” rule on the firewall, then it is trusted to enter the network.
Packet-filtering firewalls are divided into two categories: stateful and stateless. Stateless firewalls examine packets independently of one another and lack context, making them easy targets for hackers. In contrast, stateful firewalls remember information about previously passed packets and are considered much more secure.
While packet-filtering firewalls can be effective, they ultimately provide very basic protection and can be very limited—for example, they can’t determine if the contents of the request that’s being sent will adversely affect the application it’s reaching. If a malicious request that was allowed from a trusted source address would result in, say, the deletion of a database, the firewall would have no way of knowing that. Next-generation firewalls and proxy firewalls are more equipped to detect such threats.
Next-generation firewalls (NGFW)
combine traditional firewall technology with additional functionality, such as encrypted traffic inspection, intrusion prevention systems, anti-virus, and more. Most notably, it includes deep packet inspection (DPI). While basic firewalls only look at packet headers, deep packet inspection examines the data within the packet itself, enabling users to more effectively identify, categorize, or stop packets with malicious data.